Cyberbullying, how to prevent and combat it?
September 16, 2020
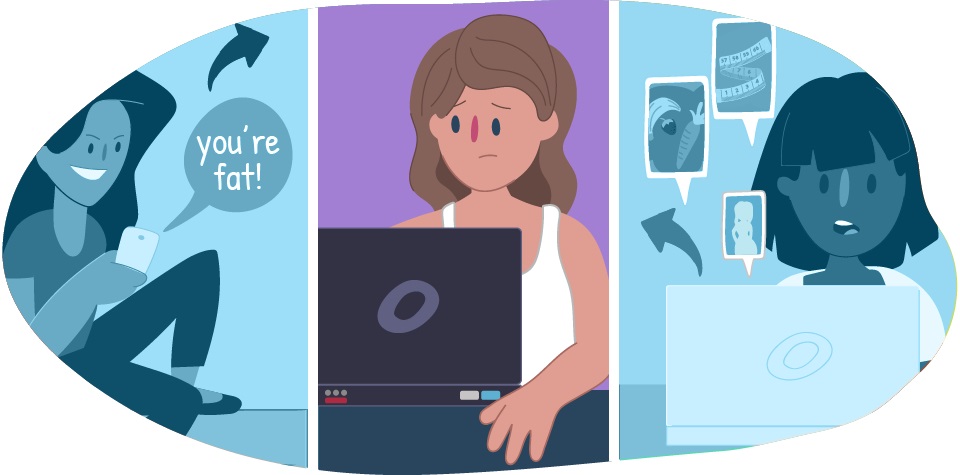
Cyberbullying is defined as the intimidation or harassment that one person (cyber-criminal) exercises against another (cyber-victim), through electronic means (Internet or text messages via cell phone). Often subjects can be cyber-victims and cyber-attackers simultaneously or, be concurrently immersed in traditional bullying. Cyberbullying invades the privacy of the home, of people assaulted at any time of the day or night, making this practice even more psychologically aggressive.
Cyberbullying usually involves intentional and repeated attacks over a period of time. The main effects are the damage to the victim’s self-esteem and dignity, which can lead to serious problems such as intense emotional stress and social rejection, among others. In the case of using digital media, the consequences can be aggravated, because they act as a speaker due to its range.
Interpersonal relationships and social networks
Interpersonal relationships are important for each of the people, because it promotes adaptation to the environment, the lack of these incites rejection, isolating themselves from other people and restricting the quality of life.
Consensus on quality of life with the following conceptual principles:
- The quality of life of people with intellectual disabilities is made up of the same factors as for other people.
- The person with intellectual disabilities experiences a quality of life when the needs are met and when he has opportunities to enrich life in the different fields and dimensions of it (personal, labor, social, among others).
- Quality of life is a construct that contains objective and subjective components, with the second being fundamental, because it is the subject himself who perceives the quality of life he is experiencing.
- Quality of life is based on individual needs, the ability to make choices and take control of one’s life.
- And finally, it is a multidimensional concept influenced by environmental and personal factors (intimate relationships, family, friends, work, neighborhood, city of residence, home, education, health, among others).
In the world there are millions of people and we are all different although we have a slight similarity with some we are not the same, the human being tries to maintain a communication with others but many times however tried you cannot please everyone, that is why the problems begin
How cyberbullying manifests
The forms it takes are very varied and are limited only by the technological expertise and imagination of the lesser stalkers, which is hopeless. Specific examples might include:
- Hang on the Internet a compromised image (real or made by photo montages) sensitive data, things that can harm or embarrass the victim and make it known in the relationship environment.
- Create a false profile or space on behalf of the victim, on social networks or forums, where certain personal events, explicit demands for sexual contacts…
- Leave offensive comments on forums or aggressively participate in chats posing as the victim so that the reactions are subsequently aimed at those who have suffered the usurpation of personality.
- Registering the email address on certain sites so that you are then a victim of spam, contacts with strangers.
- Usurp the email key to, in addition to changing it so that the rightful owner cannot consult it, read the messages that the mailbox receives in violation of privacy.
- Circulate rumors in which the victim is accused of reprehensible, offensive or unfair behavior, so that it is others who, without questioning what they read, exercise their own forms of retaliation or harassment.
- Sending threatening messages by e-mail or SMS, chasing and stalking the victim in internet locations where it is usually related causing a feeling of complete burden.
Types of cyberbullying
Within the figure of cyberbullying among minors can be given different behaviors:
Arrasement
Consists of constantly denigrating, threatening and insulting a person through social media messages, emails, WhatsApp messages or similar applications. This behavior includes putting up nicknames, sending humiliating photos or videos, or creating rumors about a person, all with the intention of other people to add to the public humiliation that is being made of the affected person and disseminate the content.
Revenge porn
“Sexting” (sending photos or videos of yourself and sexual content) has become a common behavior between teens and adults. It derives from it the so-known as revenge porn, which consists of uploading those videos or photos to the Internet or distributing them through other online media in order to get revenge on a person.
Stalking
This behavior consists of constant online tracking of a person to let them know that there is a romantic or sexual interest in it or to control all their online movements once a relationship has started.
What can be done against cyberbullying?
- If your child shows that he or she is being harassed, the first thing you have to do is talk to them. Let them know they can count on you, and that you’re going to look for measures to fix the problem. In some cases, children may need psychological help from a professional to regain self-esteem and self-confidence.
- If cyberbullying comes from schoolmates, it must be communicated to school leaders. If they don’t take action, or aren’t enough to stop the situation, you can go to the Education Inspection and file a complaint to study the case.
- In cases where these measures are not sufficient, or if the harassment does not come from peers from the same school, what you should do is go to court.
- In these situations it is important to seek specialized legal advice and start collecting all the data and evidence that can help demonstrate in a judicial process that there has actually been cyberbullying.
- The first self-protection barrier you can teach your child is to protect his or her privacy. Encourage him to use a fictitious name and a photograph of some fictional character for his social media profiles. Please do not share personal information on the Network and create strong passwords.
- Never respond to a provocation: only the situation will be aggravated. Block the aggressor from receiving their threats and report it on the social network itself.








